Free Download Pluralsight - Post-exploitation and Lateral Movements for CompTIA Pentest+
Published: 3/2025
MP4 | Video: h264, 1920x1080 | Audio: AAC, 48 KHz
Language: English | Size: 526.57 MB | Duration: 1h 28m 10s
This course teaches you how to establish persistence, execute lateral movements, exfiltrate data, and perform cleanup operations, preparing you for the CompTIA PenTest+ exam.
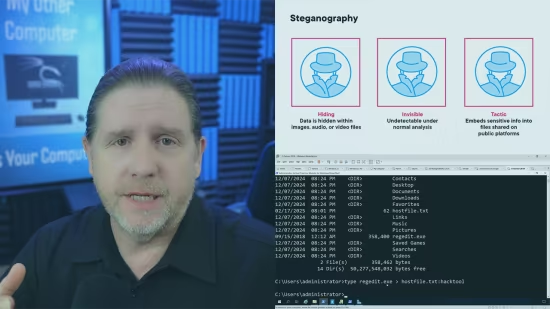
Post-exploitation techniques are critical for maintaining access, moving laterally, and extracting data in a controlled and ethical penetration testing engagement. In this course, Post-exploitation and Lateral Movements for CompTIA PenTest+, you'll gain the skills required to effectively navigate compromised environments.
First, you'll learn how to establish and maintain persistence using scheduled tasks, command-and-control frameworks, and rootkits. Next, you'll explore lateral movement techniques, such as pivoting, service enumeration, and credential dumping, using tools like Mimikatz and Impacket. Finally, you'll cover staging and exfiltration methods, as well as cleanup and restoration activities to revert changes and preserve evidence.
By the end of this course, you'll have the knowledge to execute post-exploitation techniques responsibly and effectively, fully preparing you for the CompTIA PenTest+ certification exam.
Homepage:
Code:
Bitte
Anmelden
oder
Registrieren
um Code Inhalt zu sehen!
Recommend Download Link Hight Speed | Please Say Thanks Keep Topic Live
Code:
Bitte
Anmelden
oder
Registrieren
um Code Inhalt zu sehen!